
Forcepoint TRITON AP-ENDPOINT
Stop Advanced Threats and Secure Sensitive Data for Roaming Users
Sorry, this product is no longer available, please contact us for a replacement.
Click here to jump to more pricing!
Overview:
Environment Options

Endpoint
Defend your users against data theft and sophisticated attacks when they’re at their desks or on the go.
Your employees count on maximum flexibility as they work in the office, from home or on the road, but their laptops are also vulnerable to serious threats — from their own risky behaviors or exploits devised by determined external attackers.
From a damaged reputation to regulatory fines and penalties, a data breach can have devastating consequences. Securing roaming users against threats and data theft remains a significant challenge for IT security professionals. TRITON AP-ENDPOINT protects roaming users against Advanced Threats and data theft on and off your network in an easy-to-use solution. Advanced technologies help you quickly identify and protect sensitive data and provide actionable forensic insight into attacks on endpoint devices on or off network. Forcepoint TRITON AP-ENDPOINT protects your data, allowing your mobile workforce to do business wherever and whenever they need to.
TRITON AP-ENDPOINT protects your users against data theft whether they are on or off the corporate network. Its powerful DLP capabilities enable you to secure personal data, intellectual property and other sensitive information on MacOS, Linux or Windows endpoints, and its preconfigured policies allow you to meet compliance requirements quickly and easily.
Seamless Integration for Greater Protection in the Cloud
TRITON AP-ENDPOINT is powered by the TRITON APX architecture, which eases the burden on your IT staff by including unified reporting and administrative tools for our endpoint, Web, email and DLP solutions in a single console.
Forcepoint empowers your endpoint security
- Secure sensitive data on Mac OS X and Windows endpoint devices off your network.
- Protect off-network endpoints from Advanced Threats.
- Secure inbound threats or outbound data hidden in SSL traffic from all endpoints.
- Control the use of USB storage devices by blocking or encrypting sensitive data transferred to removable media.
- Adopt cloud services like Office 365 and Box Enterprise with safety and confidence.
- Easily demonstrate security controls to auditors and executives for compliance and regulatory requirements.
Features:
- MacOS X support
- Precise data fingerprinting to identify even fragments of sensitive data
- Unified management, reporting and dashboards across all TRITON APX products
- Fingerprinting (including partial fingerprinting) support for endpoint devices on or off the network.
- Mac OS X and Windows supported endpoints.
- Protect sensitive data sent to USB devices, removable media, printers, or cloud services like Office365 and Box Enterprise.
- Portable decryption for USB/media.
- Drip DLP considers cumulative data transmission activity over time to discover small amounts of data leakage.
- Efficiently inspect HTTPS traffic with the flexibility to decide which type of SSL traffic to inspect.
- Identify Advanced Threat web activity across the entire Kill Chain on endpoints operating beyond the reach of network defenses.
- Identify high-risk employees through anomalous cumulative activity analysis compared to peer group and past behaviors.
Capabilities:
Enable off-network roaming users
Users often require access to sensitive information even while operating remotely. TRITON AP-ENDPOINT delivers the necessary data theft controls on Mac OS X and Windows laptops so you can safely empower those users. Find and secure critical data residing on endpoints, whether the user is on or off your organization’s network, including powerful data fingerprinting capabilities often lacking in endpoint DLP solutions.
Embrace innovation with safety and confidence
Meeting your customer needs and remaining competitive requires innovation and empowering your workforce with new solutions and technologies. TRITON AP-ENDPOINT helps you safely adopt new cloud services such as Office 365 or Box Enterprise with both web threat defenses and the ability to retain control of sensitive data. Users on Mac OS X and Windows, on or off the network, working anytime, anywhere, receive the full benefit of advanced threat defenses and DLP. Control the use of removable media, like USB drives, with options to block or encrypt policy-identified data. Control the flow of data to cloud services, all while innovating as needed to grow your organization.
Web security follows your roaming users
The risks from web-based attacks, including Advanced Threats, are even greater for users operating beyond your organization’s network. TRITON AP-ENDPOINT extends web security to roaming users, safely allowing them access to web-based resources. More than simple URL filtering, attack activity across the Kill Chain can be identified and blocked, even while working in a proxy-free environment. TRITON AP-ENDPOINT sees into SSL traffic to secure the Web channel for your roaming users even while using Cloud, Email, Social Media or other services that employ secure connections.
Manage easily with your existing IT staff
Staffing challenges within IT include limited headcount and finding skilled security personnel. The TRITON architecture unifies the management of Web, Email, Data, and Endpoint security, including policies that can be easily defined and deployed where needed. Quickly respond to new threats across multiple channels, including securing roaming users. Secure your sensitive IP and PII data while easily meeting your compliance and regulation requirements with and extensive library of out-of-the-box policies.
Components and Add-On Modules:
TRITON AP-ENDPOINT DLP
Forcepoint TRITON AP-ENDPOINT DLP extends OCR, ‘Drip DLP’, and other data theft controls capabilities to Mac OS X and Windows endpoints, both on and off your network. Forcepoint enables the secure sharing of data stored on removable storage using policy driven file encryption. Monitor web uploads including HTTPS as well as uploads to cloud services like Office 365 and Box Enterprise. Full integration with Outlook, Notes, and mail clients all while using the same user interface as Forcepoint’s Data, Web, Email, and Endpoint solutions.
- Discover and secure critical data from exfiltration, whether users are on or off the corporate network
- Secure MacOS, Linux and Microsoft endpoints, including protection against data loss via USB and other removable media
- Safely embrace cloud services such as Microsoft Office 365 and Box by gaining thorough visibility and control over data in the cloud
- Quickly meet compliance and regulatory requirements with an extensive library of out-of-the-box policies, and satisfy auditors with standardized or customized reporting
| TRITON AP-ENDPOINT DLP, TRITON AP-DATA & Modules | TRITON AP-DATA Discover | TRITON AP-DATA Gateway | TRITON AP-ENDPOINT DLP |
|---|---|---|---|
| ACE (Advanced Classification Engine) Real-time assessment of content, scripts, and other potential threat components. |
|||
| Behavioral File Sandboxing An additional malware analysis option activated within ACE, especially useful for zero-day malware detection. |
|||
| URL Sandboxing Modifies suspicious URLs for additional analysis when the user clicks the link. |
|||
| Scan and Remediate Supports network and cloud resources, such as Office 365 and Box Enterprise. Endpoint scanning is available with AP-ENDPOINT, sold separately |
w/Discover | ||
| OCR (Optical Character Recognition) Extract text within images for policy violation assessment |
|||
| Drip DLP Detect small amounts of data theft over extended periods of time. |
|||
| Enterprise-Class DLP Capabilities Includes advanced fingerprinting and machine learning. |
|||
| Custom-Encrypted Upload Detection Identify the use of encryption methods designed to evade DLP analysis. |
|||
| Password File Data Theft Detection Coordinate with the network to detect the illegitimate transmission of user credentials. |
|||
| MAC OS X and Windows Endpoints | |||
| USB Security Monitor, block, or force encryption of data sent to USB storage. |
|||
| Application Data Controls (ie. cut, paste, copy, screen capture) |
|||
| TRITON Unified Security Center Unified policies, dashboards, reports and more reduce the time and expertise required to achieve results. |
 Power Behind TRITON Solutions:
Power Behind TRITON Solutions:
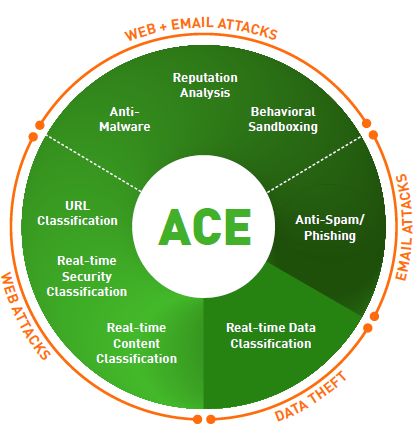
ACE (Advanced Classification Engine)
Forcepoint ACE provides real-time, inline contextual defenses for Web, Email, Data and Mobile security by using composite risk scoring and predictive analytics to deliver the most effective security available. It also provides containment by analyzing inbound and outbound traffic with data-aware defenses for industry-leading data theft protection. Classifiers for real-time security, data and content analysis — the result of years of research and development — enable ACE to detect more threats than traditional anti-virus engines every day (the proof is updated daily at http://securitylabs.forcepoint.com). ACE is the primary defense behind all Forcepoint TRITON solutions and is supported by the Forcepoint ThreatSeeker Intelligence Cloud.
Integrated set of defense assessment capabilities in 8 key areas.
- 10,000 analytics available to support deep inspections.
- Predictive security engine sees several moves ahead.
- Inline operation not only monitors, but blocks threats.
ThreatSeeker Intelligence Cloud
The ThreatSeeker Intelligence Cloud, managed by Forcepoint Security Labs, provides the core collective security intelligence for all Forcepoint security products. It unites more than 900 million endpoints, including inputs from Facebook, and, with Forcepoint ACE security defenses, analyzes up to 5 billion requests per day. This expansive awareness of security threats enables the ThreatSeeker Intelligence Cloud to offer real-time security updates that block Advanced Threats, malware, phishing attacks, lures and scams, plus provides the latest web ratings. The ThreatSeeker Intelligence Cloud is unmatched in size and in its use of ACE real-time defenses to analyze collective inputs. (When you upgrade to Web Security, the ThreatSeeker Intelligence Cloud helps reduce your exposure to web threats and data theft.)
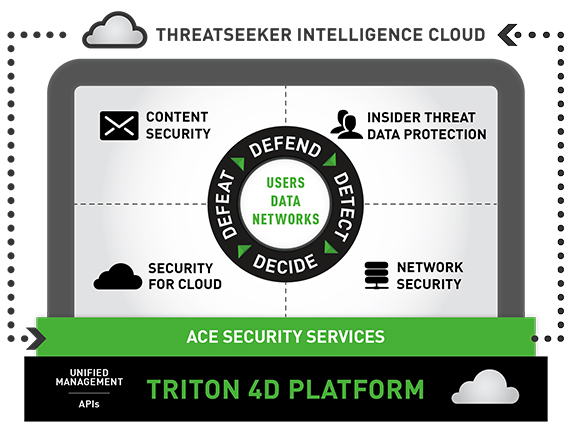
TRITON Architecture
With best-in-class security and a unified architecture, Forcepoint TRITON offers point-of-click protection with real-time, inline defenses from Forcepoint ACE. The unmatched real-time defenses of ACE are backed by Forcepoint ThreatSeeker Intelligence Cloud and the expertise of Forcepoint Security Labs researchers. The powerful result is a single, unified architecture with one unified user interface and unified security intelligence.
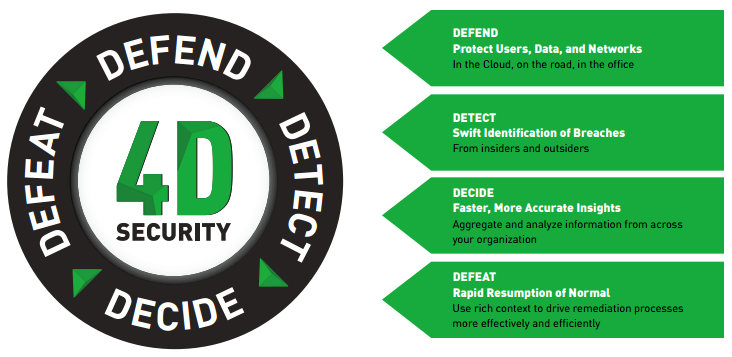
A unified, cloud-centric security platform to safeguard users, data and networks
Forcepoint’s unified, cloud-centric security platform integrates with your existing infrastructure to help you safeguard your users, data and networks. Powered by our TRITON 4D Platform, our ACE shared security services work closely with our global ThreatSeeker Intelligence Cloud to provide up-to-the-moment knowledge of the latest advanced threats that is shared across our products.
While our products are modular, integrating through our platform means our solutions can share a common security context, helping to detect suspicious activity and content sooner. The platform also provides better insights throughout the network so you take the best actions to fix breaches and reduce dwell time.
Protect your data throughout the threat lifecycle
Solutions backed by the TRITON 4D Platform
- Content Security
Forcepoint enables your employees to safely communicate and read content received over email, the web and other channels without being attacked by advanced threats. In addition, sophisticated Data Loss Prevention, integrated directly into our security gateways, helps prevent information from being accidentally or maliciously transmitted to places it doesn’t belong. - Insider Threat Data Protection
Every moment, your employees accidentally or intentionally create opportunities for breaches. Forcepoint lets you monitor user activity to identify the early warning signs of risky behavior, then detect and block attempts to move sensitive data in and out of your organization. Our solutions can automatically identify the riskiest users within an organization, based on their behaviors and on how they use data. This unique approach gathers rich context, including recording and playback of user activities before, during and after risky behaviors, giving you the data to take the right actions to protect your business. - Security for Cloud
Forcepoint’s comprehensive products enable organizations to safely move their business to the Cloud, taking advantage of the latest technologies for mobile users and distributed organizations. We enable your mobile and distributed workforces to take full advantage of Office 365, web applications and email without sacrificing the controls and security you need. Forcepoint enables you to discover confidential data stored in sanctioned business apps like Box and Salesforce, and to identify risky unsanctioned apps that users access. We even give you the ability to protect the Linux server farms running your applications by detecting potential threats without compromising the performance of your line-of-business systems. - Network Security
In today’s world, organizations are more decentralized than ever. From a single console, our next-generation firewall lets you reliably enforce security policies across your headquarters, corporate locations, divisions, branches, remote offices and even home offices. It integrates application control, sophisticated evasion prevention and an intrusion prevention system (IPS) into a single, easy-to-deploy solution.
TRITON APX
TRITON APX provides many key benefits to organizations interested in deploying the best possible protection against Advanced Threats across the “7-Stage Kill Chain.” They can be summarized in these three statements:
- Deploy Adaptive Security - Deploy adaptive security solutions for rapidly changing technology and threat landscapes.
- Protect Everywhere - The perimeter is the data. Protect critical information from theft whether on-premise, in the cloud or on mobile devices.
- Raise the Security IQ - Combat the cyber security skills shortage by providing predictive actionable intelligence across the entire threat lifecycle.

Documentation:
Download the Forcepoint TRITON AP-ENDPOINT Datasheet (.PDF)
Download the Forcepoint TRITON AP-DATA and AP-ENDPOINT Product Matrix Datasheet (.PDF)
Price Note:
- TRITON AP-DATA Discover, TRITON AP-DATA Gateway, TRITON AP-ENDPOINT DLP, Threat Protection Appliance - Endpoint, SureView Insider Threat Core and SureView Insider Threat Endpoint under 250 user band subject to approvals.
- Threat Protection Appliance - Web, Threat Protection Appliance - Email and Threat Protection for Linux under 100 user band subject to approvals.
