
Forcepoint TRITON AP-WEB
Industry Leading Protection against Advanced Threats and Data Theft
Sorry, this product is no longer available, please contact us for a replacement.
Click here to jump to more pricing!
Overview:
Environment Options

Cloud

Endpoint

Hybrid
I-Series Appliances
V-Series Appliances
X-Series Appliances
Advanced Threats involve sophisticated, multi-stage attacks with built-in techniques to evade detection while they're stealing your sensitive data. TRITON AP-WEB stops more advanced, non-signature threats to your data than any other solution – including Blue Coat, Cisco, and McAfee (Intel Security)!
Insider Threats – such as employee theft and malware that slips into your network– are just as dangerous as external ones. TRITON AP-WEB is built on a unified platform that enables all of our products to work together and provides industry-leading reporting, sandboxing and DLP capabilities. TRITON AP-WEB is the proven leader in preventing data loss, whether deployed in the Cloud, hybrid or on-premise.
Adopt Industry-Leading Protection Against Advanced Threats and Data Theft
Take advantage of world-class protection against online threats with a cloud-first solution that streamlines your enterprise security.
In today's cloud-first world, you want your organization to reap the benefits of flexibility and rapid collaboration that come with the latest technologies. But you have to do it securely to protect your reputation and enable your long-term mission.
TRITON AP-WEB gives you the Web security you need. It provides comprehensive real-time, inline protection against advanced threats that use sophisticated techniques to evade detection while they're stealing your sensitive data, as well as insider threats such as employee theft and malware that slips into your network. TRITON AP-WEB stops more advanced, non-signature threats to your data than any other solution, and it's a proven leader in SaaS Web content security.
For even greater coverage, combine TRITON AP-WEB with TRITON AP-EMAIL and Threat Protection Cloud for comprehensive all-cloud defense against Web threats.
Seamless Integration for Greater Protection in the Cloud
TRITON AP-WEB is powered by TRITON ACE and ThreatSeeker Intelligence Cloud, which work together in real time to accurately identify and classify network traffic, apply policies and detect threats. Unified management and reporting functions streamline work for your security team, giving them the context and insights they need to minimize the dwell time of attacks and prevent exfiltration of your data. The common TRITON APX architecture also makes it simple to deploy TRITON AP-WEB separately or in any combination with TRITON AP-EMAIL, TRITON AP-DATA and TRITON AP-ENDPOINT.
Customizable with the option to expand
Companies need customizable solutions to meet their needs and budgets to protect against these types of threats as they happen. TRITON AP-WEB offers real-time protection against Advanced Threats and data theft with many deployment options and modules to help you customize your Web protection package to your needs.
Whether you need protection for on-premise users or remote users, built-in data theft defenses or a solution for mobile users, TRITON AP-WEB provides the right coverage and protection you need — no more, no less.
Web Security Challenges
Most of today’s security solutions can’t address Advanced Threats as they happen. TRITON AP-WEB is advanced, real-time threat defense.
- Reduce Risk
Complex, uncoordinated, multi-vendor security deployments increase security risks. TRITON AP-WEB provides fully-integrated, advanced protection across the entire "Kill Chain." - Stop Data Theft
Most standalone DLP solutions are too complex to deploy. TRITON AP-WEB offers completely integrated, easy-todeploy DLP with industry-leading protection. - Protect a Mobile Workforce
Extend your protection seamlessly from on-premise to remote and mobile workers with the same solution.
Features and Benefits:
Benefits
- Stop Advanced Threats — TRITON AP-WEB identifies zero-day malware and other malicious activity to stop the latest advanced persistent threats.
- Prevent Data Theft — A fully-integrated, enterprise-class DLP engine simplifies data security for both internal and external threats as it streamlines compliance.
- Monitor Web Traffic — Use behavioral sandboxing for advanced threat identification with real-time code analysis.
- Serve Mobile Users — Allow seamless access to Web resources on mobile devices when they are used outside your corporate network.
Features
- Enterprise-grade DLP protection
- Highly accurate, real-time identification and classification of threats using TRITON ACE
- Real-time threat intelligence from the ThreatSeeker Intelligence Cloud, which gives visibility into current global cyber threat activity
- Unified management, reporting and dashboards across all TRITON APX products
Capabilities:
Real-time analysis for advanced threat protection
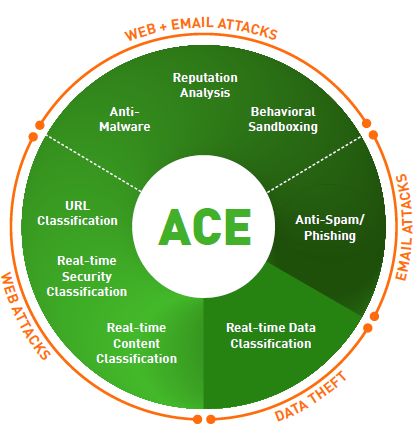
TRITON AP-WEB goes beyond anti-virus defenses by using eight defense assessment areas in a composite scoring process that uses predictive analysis with the Forcepoint ACE (Advanced Classification Engine). Multiple real-time content engines analyze full web page content, active scripts, web links, contextual profiles, files and executables.
Easy dashboard access to forensic data
The TRITON AP-WEB advanced threat dashboard provides forensic reporting on who was attacked, what data was targeted, where the data almost went and how the attack was executed. Security incidents include data theft capture when possible. Defenses analyze inbound and outbound communications.
Integrated data theft defenses
Industry-leading integrated data theft defenses (optional) detect and intercept data theft attempts and provide regulatory compliance for data loss prevention (DLP). Examples of these capabilities include detection of custom-encrypted uploads, password file data theft, slow data leaks (drip DLP), optical character recognition OCR (Optical Character Recognition) of text within images and geolocation destination awareness.
Integrated Sandboxing
Learn how to better protect your company’s assets by analyzing the behavior of malware automatically with the integrated optional sandbox service.
Other Capabilites
- Remote User Protection
Manage corporate, branch and remote users with one console and policy with the Web Cloud or Hybrid Modules. - Mobile User Protection
Extend policies and security settings to Android or iOS devices by integrating with the TRITON AP-MOBILE solution. - Flexible SSL Inspection
Granular SSL inspection capabilities let you monitor HTTPS traffic while maintaining privacy and regulatory requirements. - Granular Social Media Control
Social media controls provide great flexibility. Video controls limit or prevent viewing of viral, entertainment and surveillance videos while allowing access to YouTube Educational videos. - Application and Protocol Control
Network Agent provides granular control over hundreds of protocols and applications for an enhanced security posture. - Flexible Reporting
Four customizable dashboards, as well as more than 60 pre-defined and customizable reports, provide easy-to-read business and technical information as well as valuable insights into threat levels and more. - Multiple Deployment Options
Choose an on-premises deployment with an appliance, a hybrid deployment to protect remote users, or a complete cloudbased deployment.
Add-On Modules:
Web Cloud or Web Hybrid Module
Extend web protection and policy enforcement to remote users
Deploy TRITON AP-WEB 100% on-premise with our scalable appliance offering. Choose a 100% cloudbased deployment or deploy a hybrid network. The choice is yours, depending on your network needs.
Web DLP Module
Add a powerful, contextually aware DLP engine for added outbound protection against data theft
The Web DLP Module provides containment defenses against data theft, and enables regulatory compliance with over 1,700 pre-defined policies and templates. It also includes industry-leading protection such as Drip-DLP against slow data leaks, OCR (Optical Character Recognition) against theft of data files in image files, or Custom Encryption Detection for detection of criminally-encrypted files.
Threat Protection Cloud Module (Web Sandbox)
Integrate behavioral sandboxing for automatic and manual analysis of malware files
Analyze suspicious files in a virtual environment and look far deeper than simple file execution to provide the highest level of protection from advanced malware. Detailed forensic reporting is automatically provided when malicious files are detected.
TRITON AP-MOBILE Module
Extend policies and protection to iOS and Android users
Enable mobile devices in your workplace by extending your existing security policies to mobile devices to protect them from Advanced Threats, mobile malware, phishing attacks, spoofing and more.
| Modules | ||||
| TRITON AP-WEB & Modules | TRITON AP-WEB | Web DLP | Web Sandbox | TRITON AP-MOBILE |
|---|---|---|---|---|
| Web Proxy + SSL Explicit or transparent, multiple Auths, realm sequencing, IPv6, CC EAL 2+, FIPS 140-2 |
||||
| ACE (Advanced Classification Engine) Real-time assessment of content, scripts, and other potential threat components. |
||||
| Behavioral File Sandboxing An additional malware analysis option activated within ACE, especially useful for zero-day malware detection. |
||||
| Drip DLP Detect small amounts of data theft over extended periods of time. |
||||
| Enterprise-Class DLP Capabilities Includes advanced fingerprinting and machine learning. |
||||
| Custom-Encrypted Upload Detection Identify the use of encryption methods designed to evade DLP analysis. |
||||
| Password File Data Theft Detection Coordinate with the network to detect the illegitimate transmission of user credentials. |
||||
| OCR (Optical Character Recognition) Extract text within images for policy violation assessment. |
||||
| Advanced Threat Dashboard Forensic reporting on who, what where, how; data capture for security incidents |
||||
| Web Security and Filtering Over 120 categories supported by ACE real-time classification. |
||||
| YouTube for Education | ||||
| Social Web Controls Provide user access to social media with enforced acceptable use policies. |
||||
| Advanced Application Controls | ||||
| TRITON Unified Security Center Policies, dashboards, reports and more are available in a unified console to reduce the time and expertise required to achieve results. |
||||
| Mobile Device Security For iOS and Android devices. MDM by Airwatch, Web Security by Forcepoint, DLP through Active Sync. |
||||
 Power Behind TRITON Solutions:
Power Behind TRITON Solutions:
ACE (Advanced Classification Engine)
Forcepoint ACE provides real-time, inline contextual defenses for Web, Email, Data and Mobile security by using composite risk scoring and predictive analytics to deliver the most effective security available. It also provides containment by analyzing inbound and outbound traffic with data-aware defenses for industry-leading data theft protection. Classifiers for real-time security, data and content analysis — the result of years of research and development — enable ACE to detect more threats than traditional anti-virus engines every day (the proof is updated daily at http://securitylabs.forcepoint.com). ACE is the primary defense behind all Forcepoint TRITON solutions and is supported by the Forcepoint ThreatSeeker Intelligence Cloud.
Integrated set of defense assessment capabilities in 8 key areas.
- 10,000 analytics available to support deep inspections.
- Predictive security engine sees several moves ahead.
- Inline operation not only monitors, but blocks threats.
ThreatSeeker Intelligence Cloud
The ThreatSeeker Intelligence Cloud, managed by Forcepoint Security Labs, provides the core collective security intelligence for all Forcepoint security products. It unites more than 900 million endpoints, including inputs from Facebook, and, with Forcepoint ACE security defenses, analyzes up to 5 billion requests per day. This expansive awareness of security threats enables the ThreatSeeker Intelligence Cloud to offer real-time security updates that block Advanced Threats, malware, phishing attacks, lures and scams, plus provides the latest web ratings. The ThreatSeeker Intelligence Cloud is unmatched in size and in its use of ACE real-time defenses to analyze collective inputs. (When you upgrade to Web Security, the ThreatSeeker Intelligence Cloud helps reduce your exposure to web threats and data theft.)
TRITON Architecture
With best-in-class security and a unified architecture, Forcepoint TRITON offers point-of-click protection with real-time, inline defenses from Forcepoint ACE. The unmatched real-time defenses of ACE are backed by Forcepoint ThreatSeeker Intelligence Cloud and the expertise of Forcepoint Security Labs researchers. The powerful result is a single, unified architecture with one unified user interface and unified security intelligence.
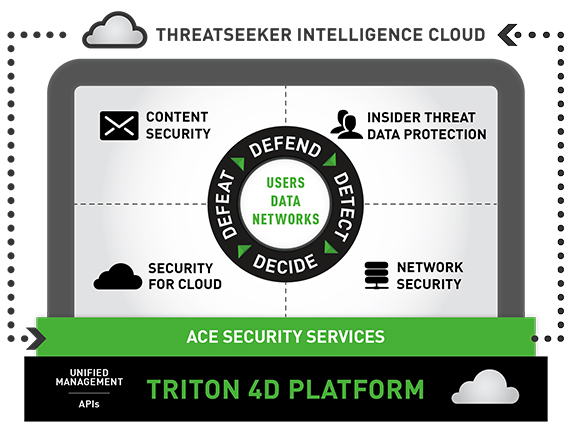
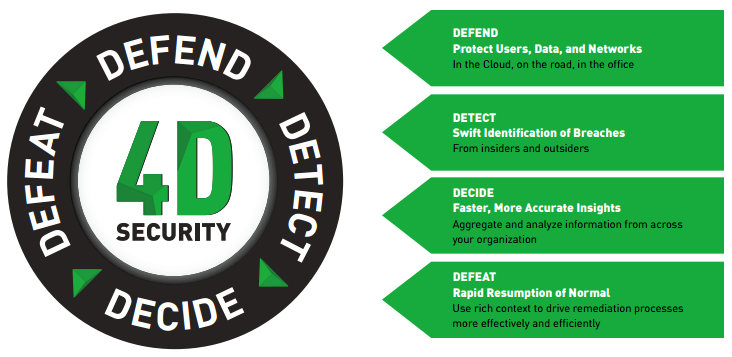
A unified, cloud-centric security platform to safeguard users, data and networks
Forcepoint’s unified, cloud-centric security platform integrates with your existing infrastructure to help you safeguard your users, data and networks. Powered by our TRITON 4D Platform, our ACE shared security services work closely with our global ThreatSeeker Intelligence Cloud to provide up-to-the-moment knowledge of the latest advanced threats that is shared across our products.
While our products are modular, integrating through our platform means our solutions can share a common security context, helping to detect suspicious activity and content sooner. The platform also provides better insights throughout the network so you take the best actions to fix breaches and reduce dwell time.
Protect your data throughout the threat lifecycle
Solutions backed by the TRITON 4D Platform
- Content Security
Forcepoint enables your employees to safely communicate and read content received over email, the web and other channels without being attacked by advanced threats. In addition, sophisticated Data Loss Prevention, integrated directly into our security gateways, helps prevent information from being accidentally or maliciously transmitted to places it doesn’t belong. - Insider Threat Data Protection
Every moment, your employees accidentally or intentionally create opportunities for breaches. Forcepoint lets you monitor user activity to identify the early warning signs of risky behavior, then detect and block attempts to move sensitive data in and out of your organization. Our solutions can automatically identify the riskiest users within an organization, based on their behaviors and on how they use data. This unique approach gathers rich context, including recording and playback of user activities before, during and after risky behaviors, giving you the data to take the right actions to protect your business. - Security for Cloud
Forcepoint’s comprehensive products enable organizations to safely move their business to the Cloud, taking advantage of the latest technologies for mobile users and distributed organizations. We enable your mobile and distributed workforces to take full advantage of Office 365, web applications and email without sacrificing the controls and security you need. Forcepoint enables you to discover confidential data stored in sanctioned business apps like Box and Salesforce, and to identify risky unsanctioned apps that users access. We even give you the ability to protect the Linux server farms running your applications by detecting potential threats without compromising the performance of your line-of-business systems. - Network Security
In today’s world, organizations are more decentralized than ever. From a single console, our next-generation firewall lets you reliably enforce security policies across your headquarters, corporate locations, divisions, branches, remote offices and even home offices. It integrates application control, sophisticated evasion prevention and an intrusion prevention system (IPS) into a single, easy-to-deploy solution.
TRITON APX
TRITON APX provides many key benefits to organizations interested in deploying the best possible protection against Advanced Threats across the “7-Stage Kill Chain.” They can be summarized in these three statements:
- Deploy Adaptive Security - Deploy adaptive security solutions for rapidly changing technology and threat landscapes.
- Protect Everywhere - The perimeter is the data. Protect critical information from theft whether on-premise, in the cloud or on mobile devices.
- Raise the Security IQ - Combat the cyber security skills shortage by providing predictive actionable intelligence across the entire threat lifecycle.

Documentation:
Download the Forcepoint TRITON AP-WEB Datasheet (.PDF)
Download the Forcepoint TRITON AP-WEB Product Matrix Datasheet (.PDF)
Price Note:
- TRITON AP-MOBILE requires either Web Cloud Module or Web Hybrid Module when added to TRITON AP-WEB.
