
Forcepoint TRITON AP-EMAIL
Stop Advanced, Targeted Attacks, Identify High Risk Users and Control Insider Threats
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
Click here to jump to more pricing!
Overview:
Environment Options

Cloud

Hybrid
V-Series Appliances
X-Series Appliances
Advanced Threats blend Web and email elements throughout multi-stage cyberattacks to probe for the weakest channel of attack, but this strategy also presents multiple opportunities to stop those attacks before possible breaches occur. TRITON AP-EMAIL secures the communication channel most often used in the early stages of an APT or other advanced attack to identify targeted threats as well as high-risk users and Insider Threats while empowering mobile workers and safe adoption of new technologies like Microsoft Office 365.
We live in a cloud-first world, with bold advances in technology constantly changing the ways we communicate and collaborate. Yet email remains the backbone of productivity, and it demands strong protection so your organization can press ahead with its work.
TRITON AP-EMAIL gives you the security you need by protecting you against multi-stage advanced threats that often exploit email to penetrate your IT environment. It applies real-time behavioral sandboxing, enterprise-grade DLP and other advanced defense technologies to identify targeted attacks, high-risk users and insider threats. TRITON AP-EMAIL monitors outbound email to prevent leaks of sensitive information, and it empowers your workers — in the office or on the road — to safely adopt technologies like Microsoft Office 365.
Seamless Integration for Greater Protection in the Cloud
TRITON AP-EMAIL is powered by TRITON ACE and ThreatSeeker Intelligence Cloud, which work together in real time to accurately identify and classify network traffic, apply policies and detect threats. Unified management and reporting functions streamline work for your security team, giving them the context and insights they need to minimize the dwell time of attacks and prevent exfiltration of your data. The common TRITON APX architecture also makes it simple to deploy TRITON AP-EMAIL separately or in any combination with TRITON AP-WEB, TRITON AP-DATA and TRITON AP-ENDPOINT.
Maximize your use and safety of email
TRITON AP-EMAIL identifies targeted attacks, high-risk users and Insider Threats while empowering mobile workers and the safe adoption of new technologies like Office 365 and Box Enterprise. From inbound attack activity to outbound data theft or botnet communication attempts, Forcepoint TRITON Email Security protects email communications as part of a complete TRITON APX defense against APTs and other Advanced Threats.
Email Security Challenges
- APTs commonly use email for early stages in their advanced attacks.
- Email must do more to address data theft and Insider Threats.
- Businesses need to adopt Office 365 and other services to expand and compete.
- Risky user habits can easily lead to security breaches and data loss.
Features and Benefits:
Benefits
- Stop targeted attacks and the early stages of advanced persistent threats
- Secure sensitive data against theft from external attacks and insider threats
- Safely adopt cloud technologies such as Microsoft Office 365
- Identify high-risk user behavior and educate users to improve threat awareness
- Deploy with AP-WEB for complete, effective Content Security
Features
- Cloud, on-premise or hybrid deployment
- Enterprise-grade DLP protection
- Highly accurate, real-time identification and classification of threats using TRITON ACE
- Real-time threat intelligence from the Forcepoint ThreatSeeker Intelligence Cloud, which gives visibility into current global cyber threat activity
- Unified management, reporting and dashboards across all TRITON APX products
- Advanced options for email encryption, archiving, image analysis and more
Capabilities:
Stop APT and other advanced targeted threats
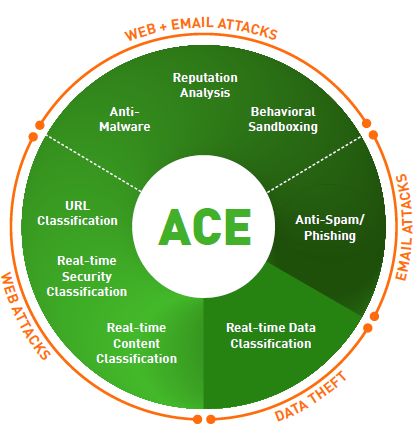
The Forcepoint ACE (Advanced Classification Engine) is at the heart of all TRITON solutions and identifies malicious lures, exploit kits, emerging threats, botnet communications and other advanced threat activity across the Kill Chain. This enables TRITON AP-EMAIL to identify the early stages of an attack. With its powerful malware assessment capabilities that include a fully-integrated, file behavioral sandboxing, it can even identify Zero-day malware threats.
Secure sensitive data against external attacks and insider threats
To prepare for a malicious Insider Threat or the potentially successful cyberattack, it’s vital that outbound communications be monitored. This is also necessary both for data theft compliance needs as well as for business requirements. Only Forcepoint provides the technology to stop data infiltration and exfiltration with capabilities such as:
- OCR (Optical Character Recognition scanning to identify sensitive data hidden in images such as scanned documents or screen shots.
- Encrypted file detection to recognize custom encrypted files designed to defy identification.
- Drip DLP monitoring to identify where sensitive data is leaked in small quantities over time.
Safely adopt new technologies like Office 365 and box enterprise while supporting your roaming workforce
IT departments are strained to maintain current systems while supporting an increasingly mobile workforce and the demands to adopt new technologies like Office 365. TRITON AP-EMAIL provides industry-leading capabilities that leverage systems and other information to control communications, such as preventing total access to sensitive email attachments on vulnerable mobile devices, while permitting full access on fully-secured laptops. These inbound and outbound defenses are all supported on Office 365.
Identify "High-Risk" user behavior and educate users to improve awareness
The rich data collections in TRITON AP-EMAIL are used by a number of policies to report and identify systems that may require special IT attention. They generate a report on a number of Indicators of Compromise to identify infected systems and more proactive reports on suspicious behavior, or even “disgruntled employee” activity as potential Insider Threats. User feedback capabilities help educate employees as mistakes are made, helping them to better learn and understand safe email best practices.
Add-On Modules:
Email Cloud or Email Hybrid Module
Leverage cloud services for performance and scalability
Combine on-premise threat defenses with cloud-based prefiltering services to preserve bandwidth with industry-leading anti-spam SLA’s. Or choose a 100% Cloud deployment of all TRITON AP-EMAIL services.
Email DLP Module
Block data theft with enterprise-class content-aware DLP
Prepare for the Insider Threat and malware data theft, achieve compliance goals and further mitigate the risk to personal information or IP. Advanced capabilities detect data theft concealed in images or custom-encrypted files, or even transmitted in small amounts over time to evade detection.
Threat Protection Cloud Module (Email Sandbox)
Integrate behavioral sandboxing for additional malware assessment
Supplement Forcepoint ACE analytics with an integrated file sandbox for additional deep inspection, and take advantage of behavioral analysis in a virtual environment to uncover the malicious behaviour of Zeroday and other advanced malware. Test files automatically or manually to generate detailed forensics.
Email Encryption Module
Ensure the confidentiality of sensitive communications
The Forcepoint Email Encryption Module is a policy-driven technology that enables secure delivery of email communications. It eliminates the traditional barriers of cost and complexity by offering easy administration, without complex key management or additional hardware.
Image Analysis Module
Identify explicit images to enforce acceptable use and compliance
The Forcepoint Image Analysis Module allows employers to take proactive measures to monitor, educate and enforce the company email policy in regard to explicit or pornographic image attachments.
| Modules | ||||
| TRITON AP-EMAIL & Modules | TRITON AP-EMAIL | Email DLP | Email Sandbox | Email Encryption |
|---|---|---|---|---|
| ACE (Advanced Classification Engine) Real-Time security, content and data classifications, anti-malware engines, contextual reputation analysis, URL classification, anti-spam/spear-phishing protection, sandboxing analysis |
||||
| Behavioral File Sandboxing An additional malware analysis option activated within ACE, especially useful for zero-day malware detection. |
||||
| URL Sandboxing Modifies suspicious URLs for additional analysis when the user clicks the link. |
||||
| Phishing Education and Reporting Provide real-time, interactive phishing education by disarming phishing threats to serve as real-life examples, making the threat personal for users. Admin tracking and reporting improve security profiles. |
||||
| Enterprise-Class DLP Engine With unique capabilities including OCR, Drip DLP, and destination geo location awareness. |
||||
| Specialized Data Theft Defenses Identify custom encrypted uploads & password data theft. |
||||
| High Risk User Identification Trends and past behavior is analyzed to identify users that may pose a risk of data theft or loss |
||||
| Advanced Threat Dashboard Forensic reporting on who, what where, how; data capture for security incidents. |
||||
| Spam Detection Accurate spam blocking with very low false positives, with options for prefiltering email in the cloud and industry leading SLAs. |
||||
| Park and Pull Email Encryption Secure email communications with 3rd parties. Park and Pull encryption triggered by policy. |
||||
| Push Style Email Encryption Seamlessly secure email communications with 3rd parties using push style Identity-Based Encryption (IBE) triggered by policy. |
||||
| TRITON Unified Security Center Unified policies, dashboards, reports and more reduce the time and expertise required to achieve results. |
||||
 Power Behind TRITON Solutions:
Power Behind TRITON Solutions:
ACE (Advanced Classification Engine)
Forcepoint ACE provides real-time, inline contextual defenses for Web, Email, Data and Mobile security by using composite risk scoring and predictive analytics to deliver the most effective security available. It also provides containment by analyzing inbound and outbound traffic with data-aware defenses for industry-leading data theft protection. Classifiers for real-time security, data and content analysis — the result of years of research and development — enable ACE to detect more threats than traditional anti-virus engines every day (the proof is updated daily at http://securitylabs.forcepoint.com). ACE is the primary defense behind all Forcepoint TRITON solutions and is supported by the Forcepoint ThreatSeeker Intelligence Cloud.
Integrated set of defense assessment capabilities in 8 key areas.
- 10,000 analytics available to support deep inspections.
- Predictive security engine sees several moves ahead.
- Inline operation not only monitors, but blocks threats.
ThreatSeeker Intelligence Cloud
The ThreatSeeker Intelligence Cloud, managed by Forcepoint Security Labs, provides the core collective security intelligence for all Forcepoint security products. It unites more than 900 million endpoints, including inputs from Facebook, and, with Forcepoint ACE security defenses, analyzes up to 5 billion requests per day. This expansive awareness of security threats enables the ThreatSeeker Intelligence Cloud to offer real-time security updates that block Advanced Threats, malware, phishing attacks, lures and scams, plus provides the latest web ratings. The ThreatSeeker Intelligence Cloud is unmatched in size and in its use of ACE real-time defenses to analyze collective inputs. (When you upgrade to Web Security, the ThreatSeeker Intelligence Cloud helps reduce your exposure to web threats and data theft.)
TRITON Architecture
With best-in-class security and a unified architecture, Forcepoint TRITON offers point-of-click protection with real-time, inline defenses from Forcepoint ACE. The unmatched real-time defenses of ACE are backed by Forcepoint ThreatSeeker Intelligence Cloud and the expertise of Forcepoint Security Labs researchers. The powerful result is a single, unified architecture with one unified user interface and unified security intelligence.
A unified, cloud-centric security platform to safeguard users, data and networks
Forcepoint’s unified, cloud-centric security platform integrates with your existing infrastructure to help you safeguard your users, data and networks. Powered by our TRITON 4D Platform, our ACE shared security services work closely with our global ThreatSeeker Intelligence Cloud to provide up-to-the-moment knowledge of the latest advanced threats that is shared across our products.
While our products are modular, integrating through our platform means our solutions can share a common security context, helping to detect suspicious activity and content sooner. The platform also provides better insights throughout the network so you take the best actions to fix breaches and reduce dwell time.
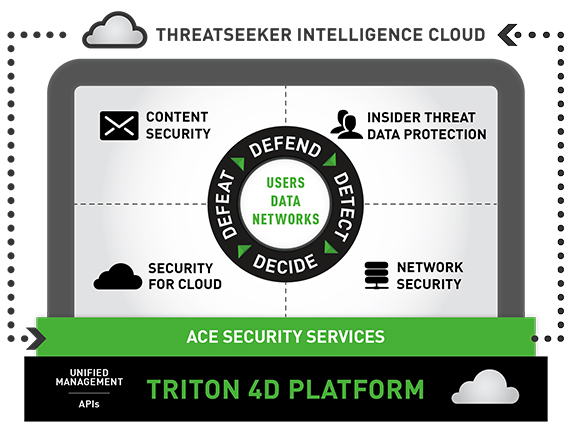
Protect your data throughout the threat lifecycle
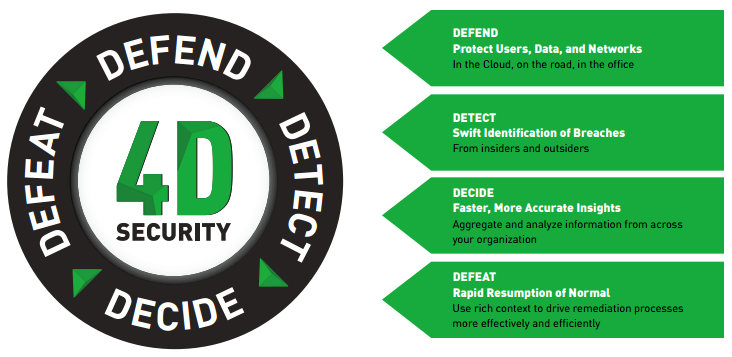
Solutions backed by the TRITON 4D Platform
- Content Security
Forcepoint enables your employees to safely communicate and read content received over email, the web and other channels without being attacked by advanced threats. In addition, sophisticated Data Loss Prevention, integrated directly into our security gateways, helps prevent information from being accidentally or maliciously transmitted to places it doesn’t belong. - Insider Threat Data Protection
Every moment, your employees accidentally or intentionally create opportunities for breaches. Forcepoint lets you monitor user activity to identify the early warning signs of risky behavior, then detect and block attempts to move sensitive data in and out of your organization. Our solutions can automatically identify the riskiest users within an organization, based on their behaviors and on how they use data. This unique approach gathers rich context, including recording and playback of user activities before, during and after risky behaviors, giving you the data to take the right actions to protect your business. - Security for Cloud
Forcepoint’s comprehensive products enable organizations to safely move their business to the Cloud, taking advantage of the latest technologies for mobile users and distributed organizations. We enable your mobile and distributed workforces to take full advantage of Office 365, web applications and email without sacrificing the controls and security you need. Forcepoint enables you to discover confidential data stored in sanctioned business apps like Box and Salesforce, and to identify risky unsanctioned apps that users access. We even give you the ability to protect the Linux server farms running your applications by detecting potential threats without compromising the performance of your line-of-business systems. - Network Security
In today’s world, organizations are more decentralized than ever. From a single console, our next-generation firewall lets you reliably enforce security policies across your headquarters, corporate locations, divisions, branches, remote offices and even home offices. It integrates application control, sophisticated evasion prevention and an intrusion prevention system (IPS) into a single, easy-to-deploy solution.
TRITON APX
TRITON APX provides many key benefits to organizations interested in deploying the best possible protection against Advanced Threats across the “7-Stage Kill Chain.” They can be summarized in these three statements:
- Deploy Adaptive Security - Deploy adaptive security solutions for rapidly changing technology and threat landscapes.
- Protect Everywhere - The perimeter is the data. Protect critical information from theft whether on-premise, in the cloud or on mobile devices.
- Raise the Security IQ - Combat the cyber security skills shortage by providing predictive actionable intelligence across the entire threat lifecycle.

Documentation:
Download the Forcepoint TRITON AP-EMAIL Datasheet (.PDF)
Download the Forcepoint TRITON AP-EMAIL Product Matrix Datasheet (.PDF)
Price Note:
- Email Encryption Module requires either Email Cloud Module or Email Hybrid Module when added to TRITON AP-EMAIL.
- Subscriptions to Image Analysis Module can be purchased with TRITON AP-EMAIL, TRITON DATA Gateway or TRITON DATA Discover. If purchasing subscriptions to multiple eligible products, Image Analysis Module should only be added once. Since Image Analysis Module will apply to all eligible products, the module user count must match the user count of AP-EMAIL, AP-DATA Gateway, or AP-DATA Discover, whichever is higher.
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
- Pricing per user for quantities 501-1,000
Get a Quote!
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
- Pricing per user for quantities 501-1,000
Get a Quote!
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
- Pricing per user for quantities 501-1,000
Get a Quote!
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
- Pricing per user for quantities 501-1,000
Get a Quote!
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
- Pricing per user for quantities 501-1,000
Get a Quote!
- Pricing per user for quantities 25-100
Get a Quote!
- Pricing per user for quantities 101-250
Get a Quote!
- Pricing per user for quantities 251-500
Get a Quote!
